DoorDash Supply-Chain Attack - Secplicity - Security Simplified
Por um escritor misterioso
Descrição
DoorDash is a popular food delivery service – and very convenient if I say so myself. However, in the seemingly never-ending trend of cyber attacks, DoorDash, too, fell victim to a supply-chain attack. Earlier this month, DoorDash identified unusual activity via a third-party service. They immediately launched an investigation and have consulted with outside agencies. […]

Software supply chain attacks: why every link matters – Sysdig
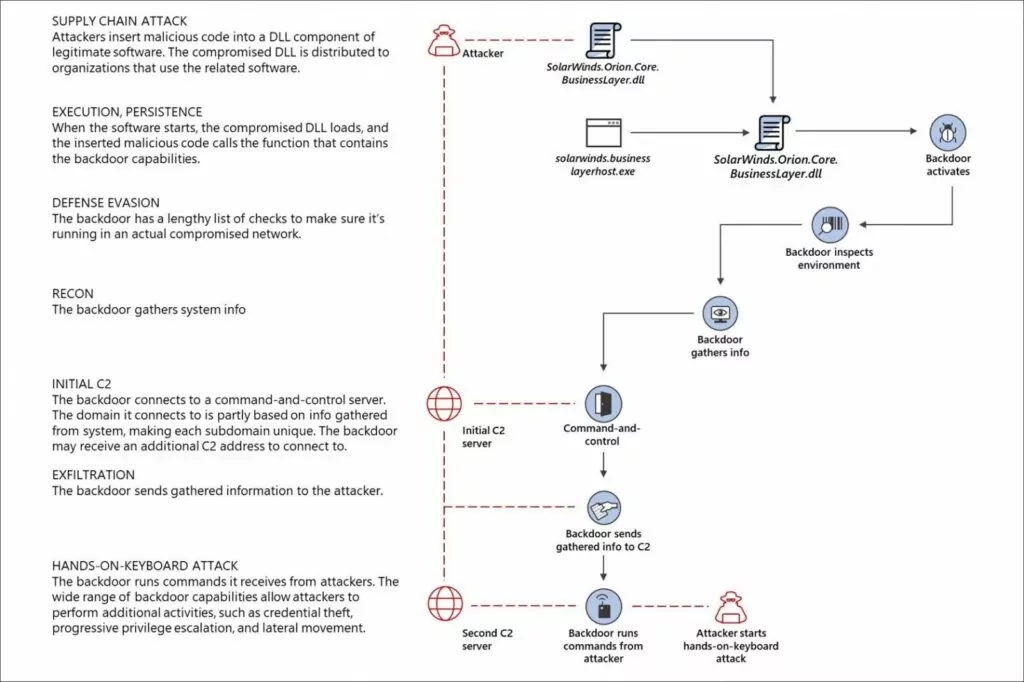
The 8 Key Lessons From the SolarWinds Attacks - SOCRadar® Cyber Intelligence Inc.

SAP Supply Chain Attack < Security News

Beware of growing software supply chain attacks
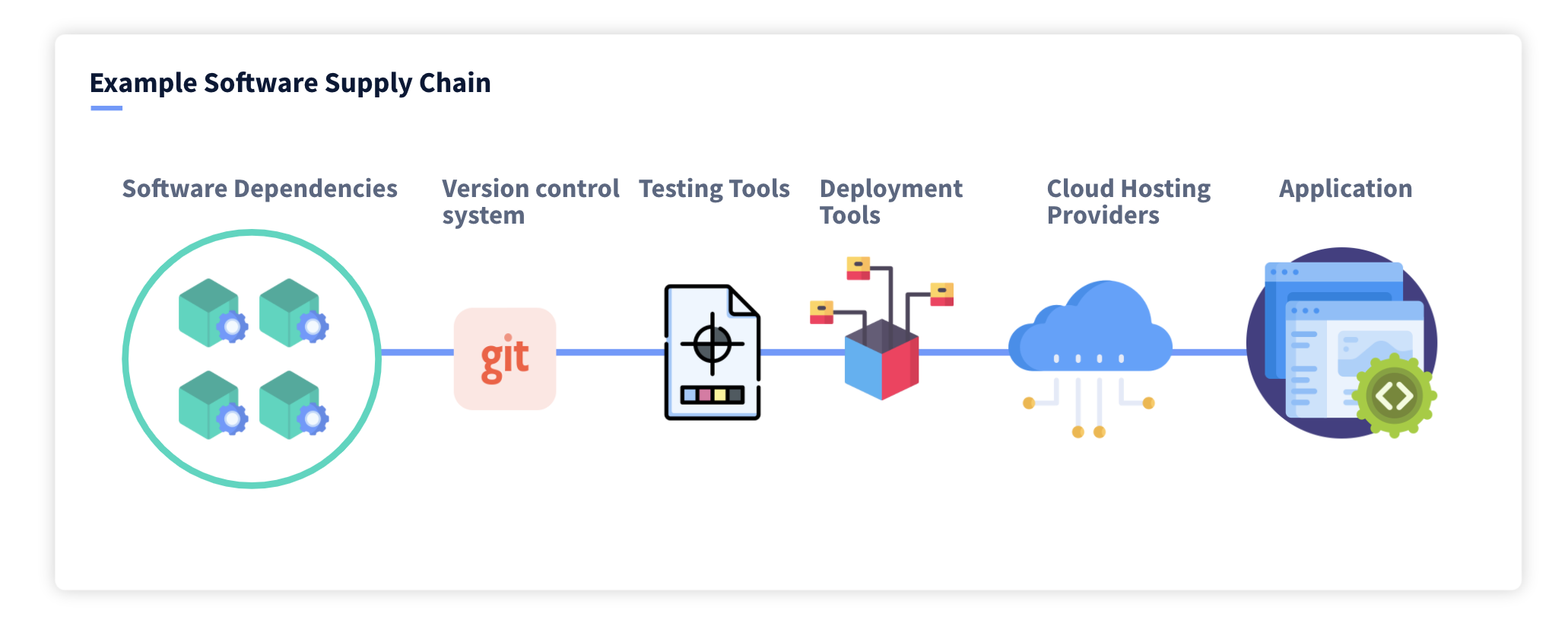
Supply Chain Attacks: 6 Steps to protect your software supply chain
Software supply chain attacks: why every link matters – Sysdig
Supply Chain Attacks: The Gift That Keeps on Giving

How to Identify and Prevent Supply Chain Attacks?
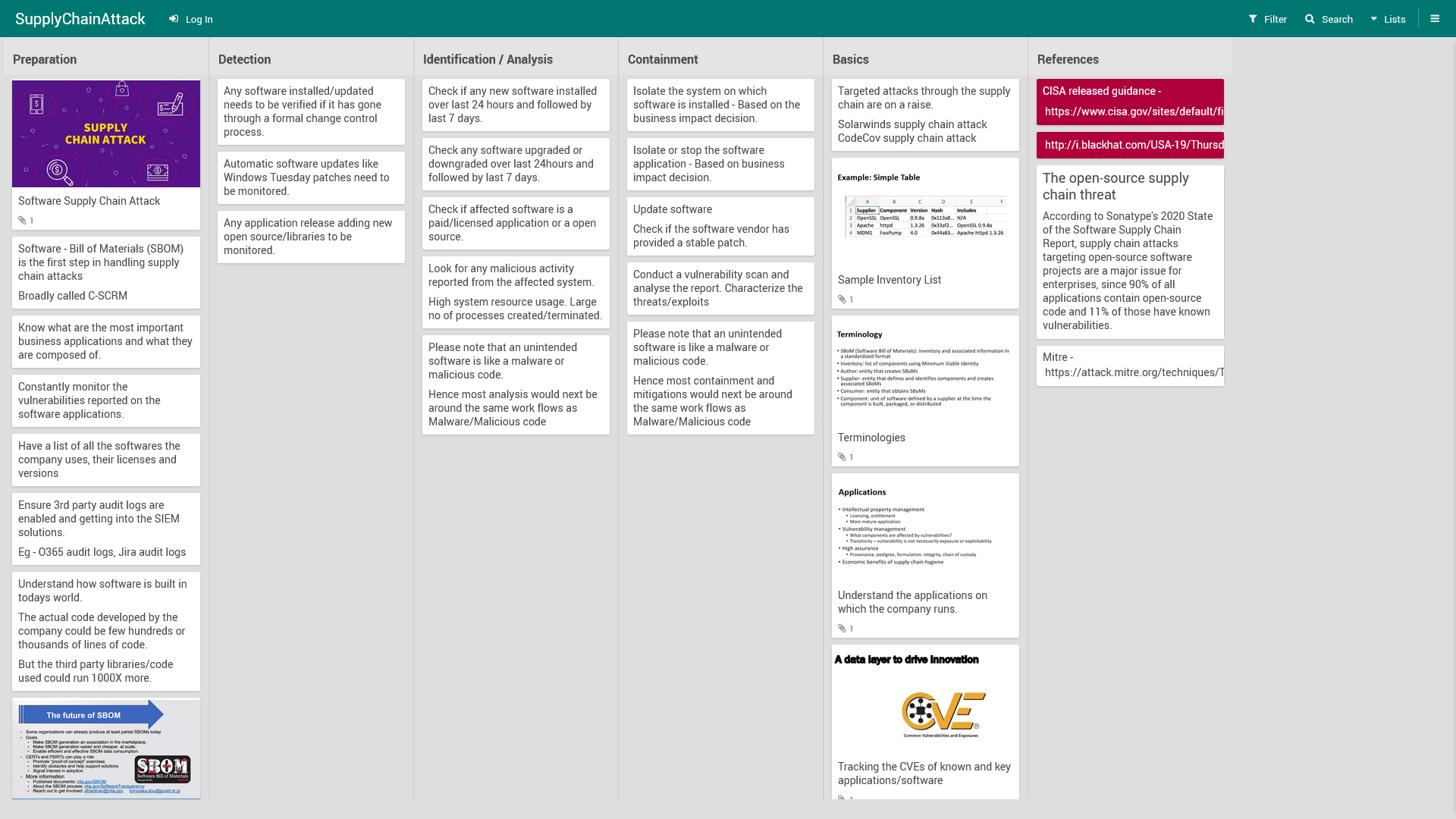
Software Supply chain attack Playbook

Supply Chain Attack Examples And Prevention Measures

Mitigating The Risk Of Supply Chain Attacks In The Age Of Cloud Computing
Software Supply Chain Attacks: An Illustrated Typological Review – Center for Security Studies

SAP Supply Chain Attack < Security News

SAP Supply Chain Attack < Security News
de
por adulto (o preço varia de acordo com o tamanho do grupo)