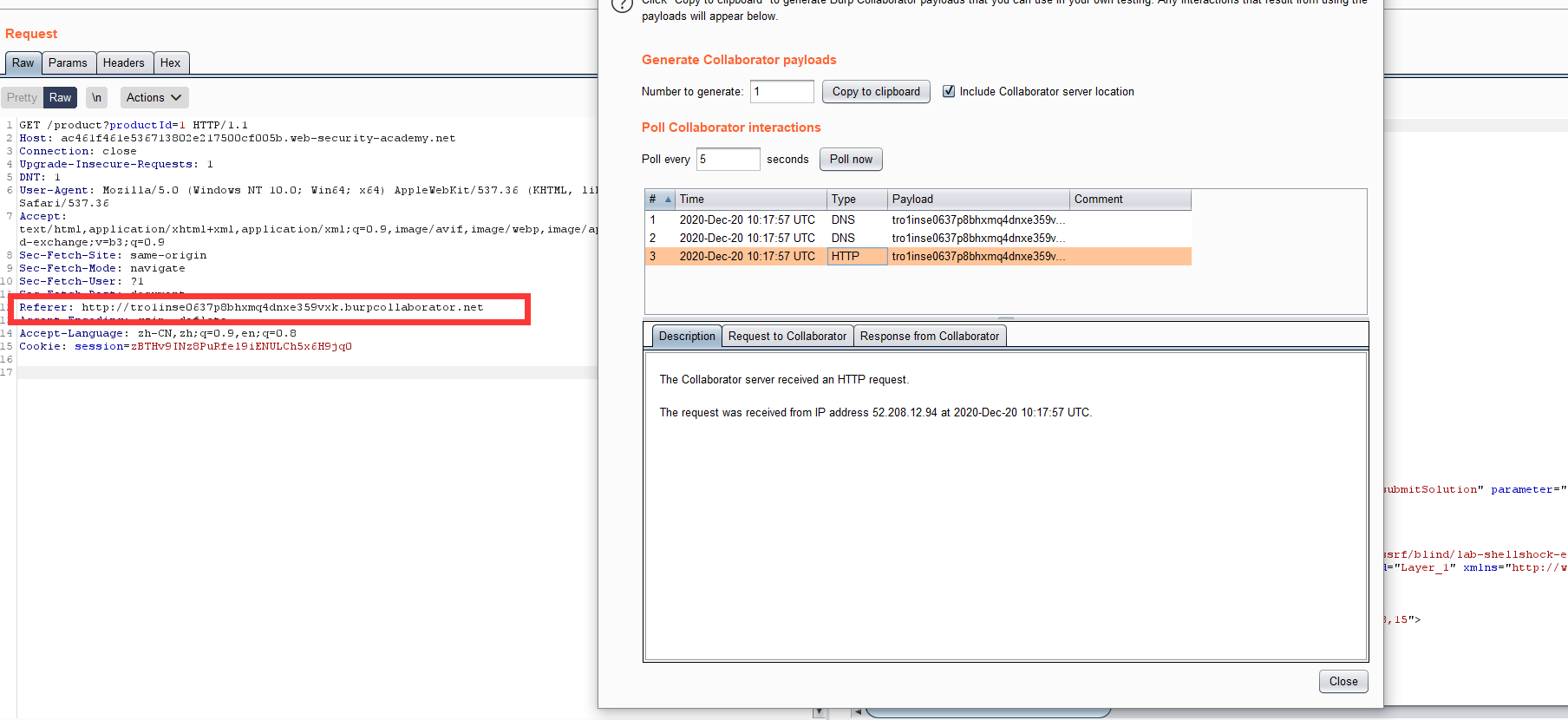
Lab: Blind SSRF with Shellshock exploitation
Por um escritor misterioso
Descrição
This site uses analytics software which fetches the URL specified in the Referer header when a product page is loaded. To solve the lab, use this

A GUIDE TO SERVER SIDE REQUEST FORGERY(SSRF) » Securityboat

Free Cybersecurity & Hacking Training
Portswigger web security academy:Server-side request forgery

TryHackMe Advent of Cyber 2 [2020]

Penetration Testing Step 3 – Blind SSRF attack với hàng độc out-of

SSRF(服务器跨站请求伪造)基础知识- lca
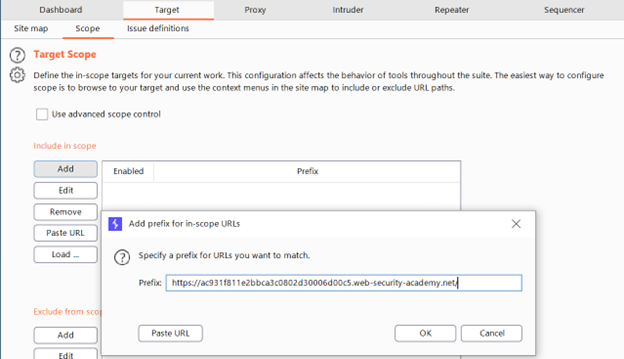
Penetration Testing Step 3 – Blind SSRF attack với hàng độc out-of

PortSwigger SSRF Labs. Hey all! This write-up is about my…
SSRF (Server Side Request Forgery) - HackTricks - Boitatech

Web Security Academy Series Course
portswigger/README.md at master · roberson-io/portswigger · GitHub

Attacking Common Applications Course
Cracking the lens: targeting HTTP's hidden attack-surface

PortSwigger - All Labs - Web Security Academy, PDF
de
por adulto (o preço varia de acordo com o tamanho do grupo)