Malware analysis Malicious activity
Por um escritor misterioso
Descrição
Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware: 9781788392501: A,

Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware
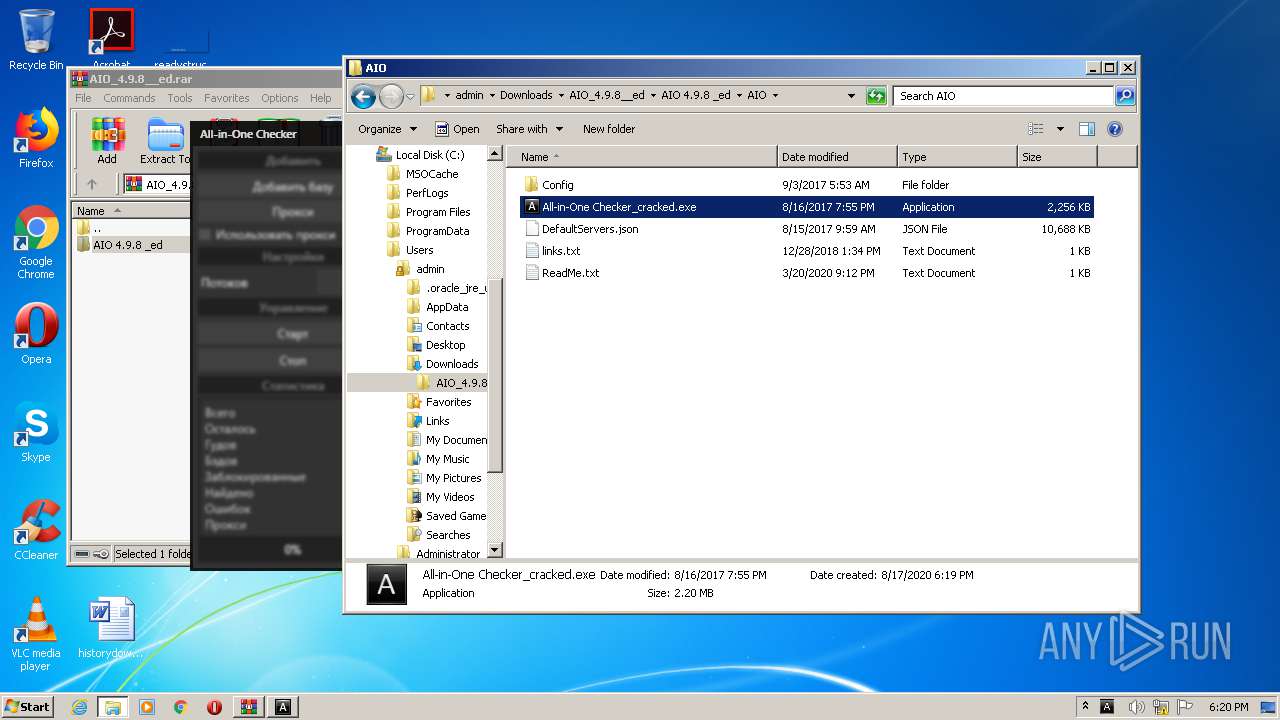
Malware analysis AIO_4.9.8__ed.rar Malicious activity

Malware Analysis Benefits Incident Response

Detail procedure of malware analysis

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware analysis tt.7z Malicious activity
Malicious URL Scanner, Scan URLs for Malware

Dynamic malware analysis [34]
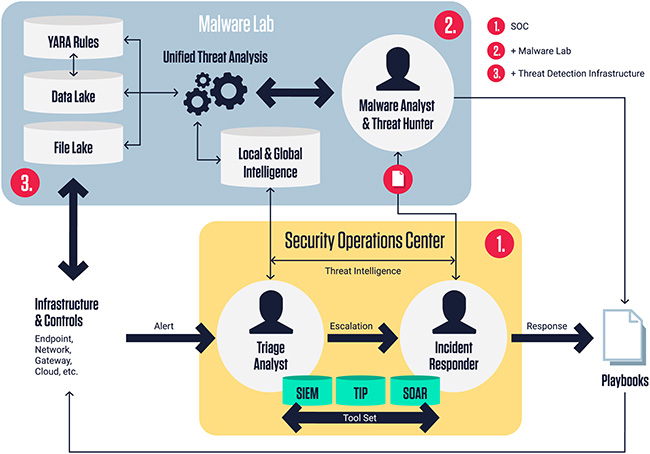
ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files - Help Net Security

What is Malware? Definition, Types, Prevention - TechTarget

How to Do Malware Analysis?

Malware analysis CQChallenge5.zip Malicious activity

What to Include in a Malware Analysis Report

Complex 'NKAbuse' Malware Uses Blockchain to Hide on Linux, IoT Machines
de
por adulto (o preço varia de acordo com o tamanho do grupo)