Malware analysis Malicious activity
Por um escritor misterioso
Descrição
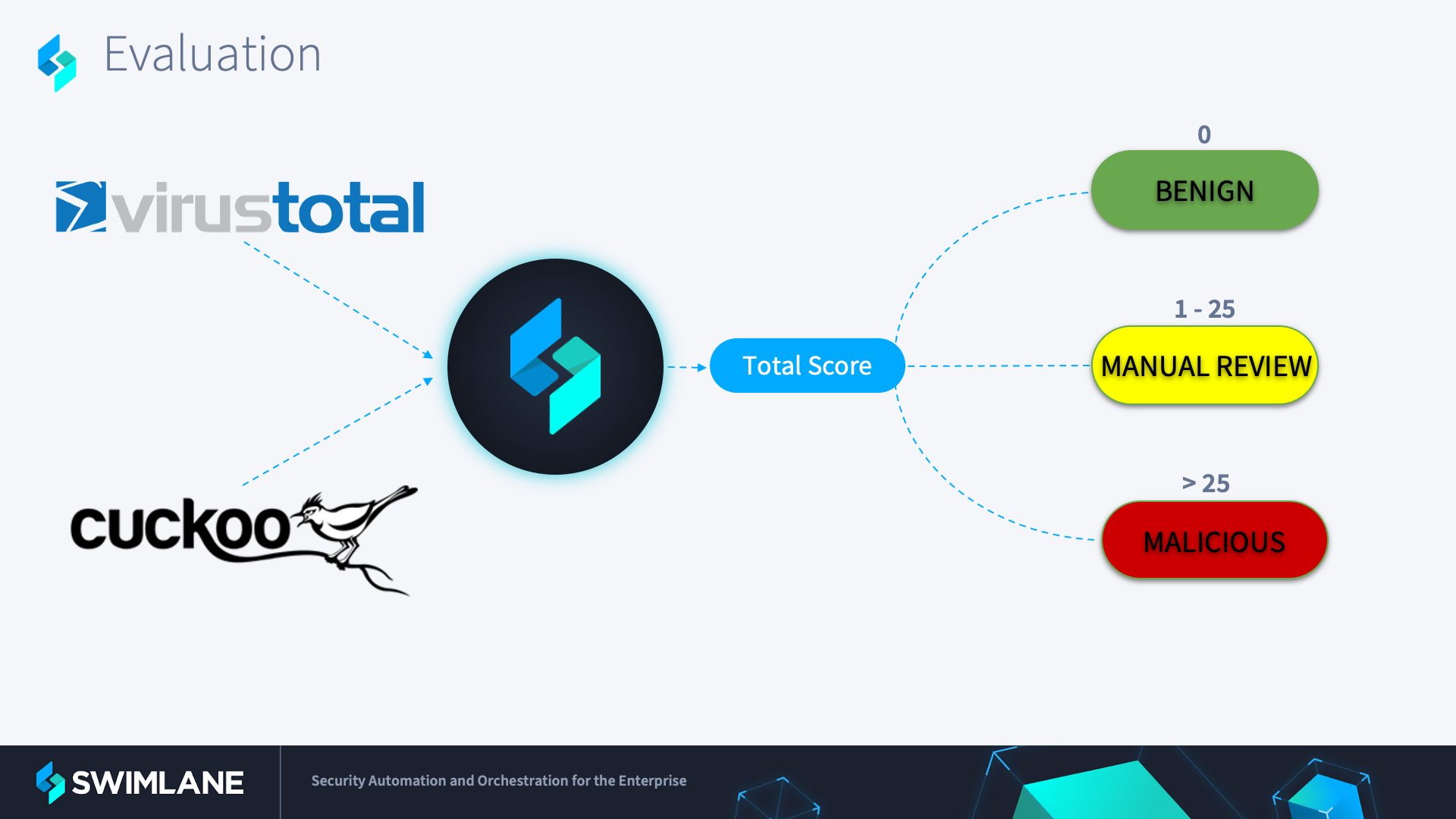
Automated Malware Analysis with Low-Code Security Automation

Dynamic malware analysis [34]

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious
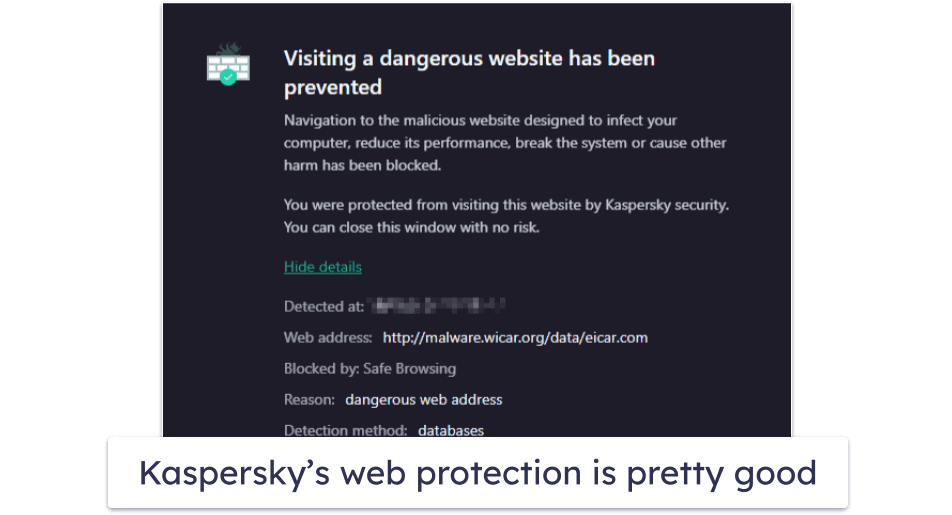
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Cybersecurity News, Insights and Analysis

Mastering Malware Analysis
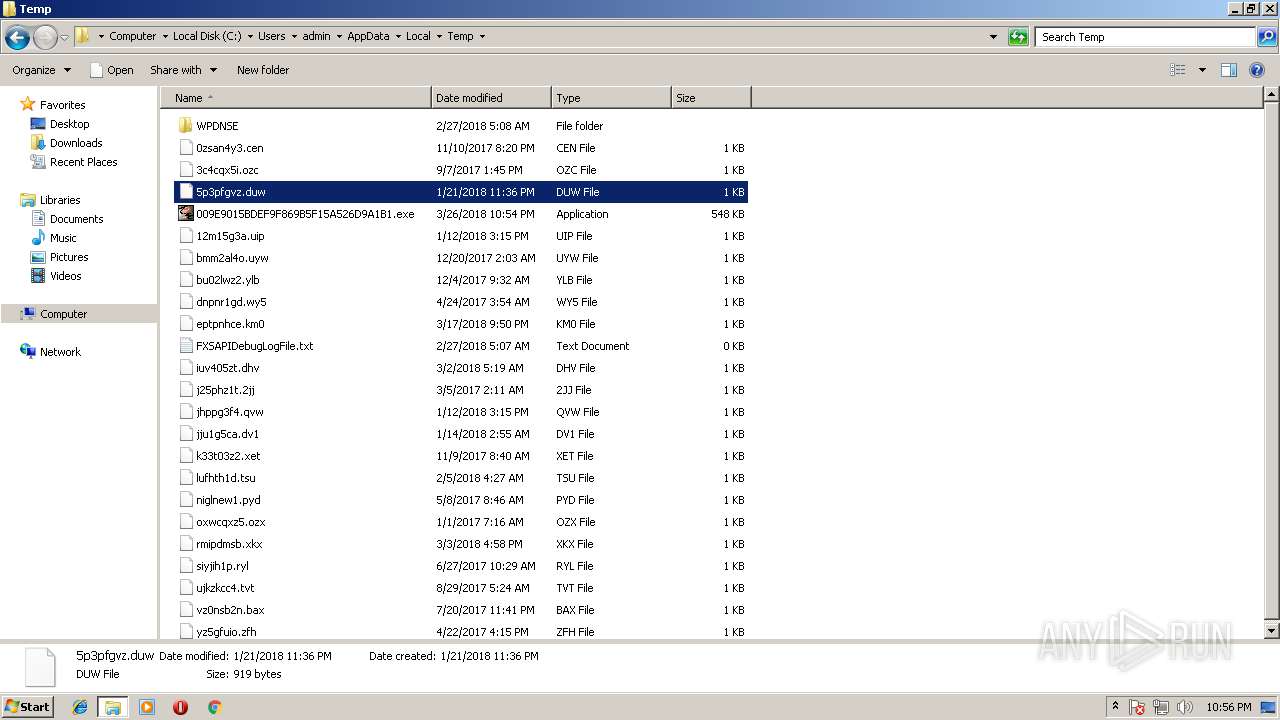
Malware analysis 009E9015BDEF9F869B5F15A526D9A1B1 Malicious

Malware analysis CQChallenge5.zip Malicious activity

AV-TEST Confirms Skyhigh Security Service Edge Delivers Superior

What is Malware? Definition, Types, Prevention - TechTarget
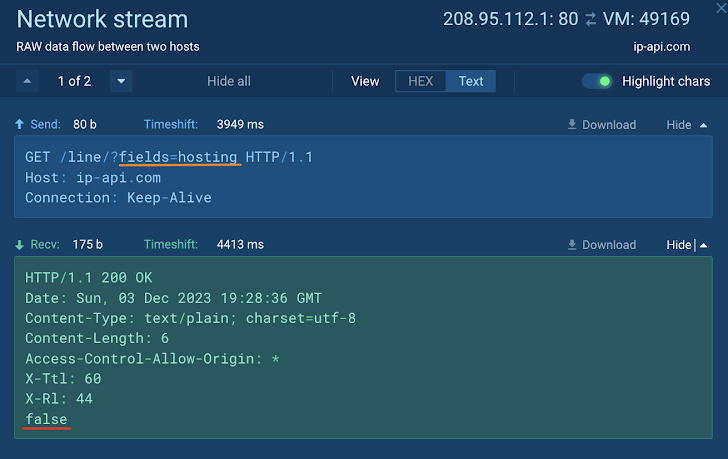
How to Analyze Malware's Network Traffic in A Sandbox

Routers Roasting on an Open Firewall: the KV-botnet Investigation
de
por adulto (o preço varia de acordo com o tamanho do grupo)