Malware analysis Malicious activity
Por um escritor misterioso
Descrição
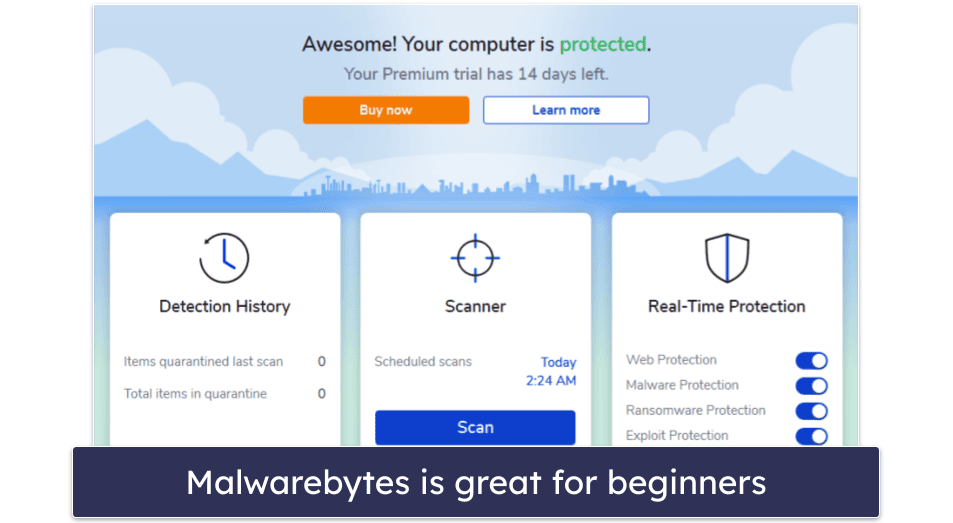
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
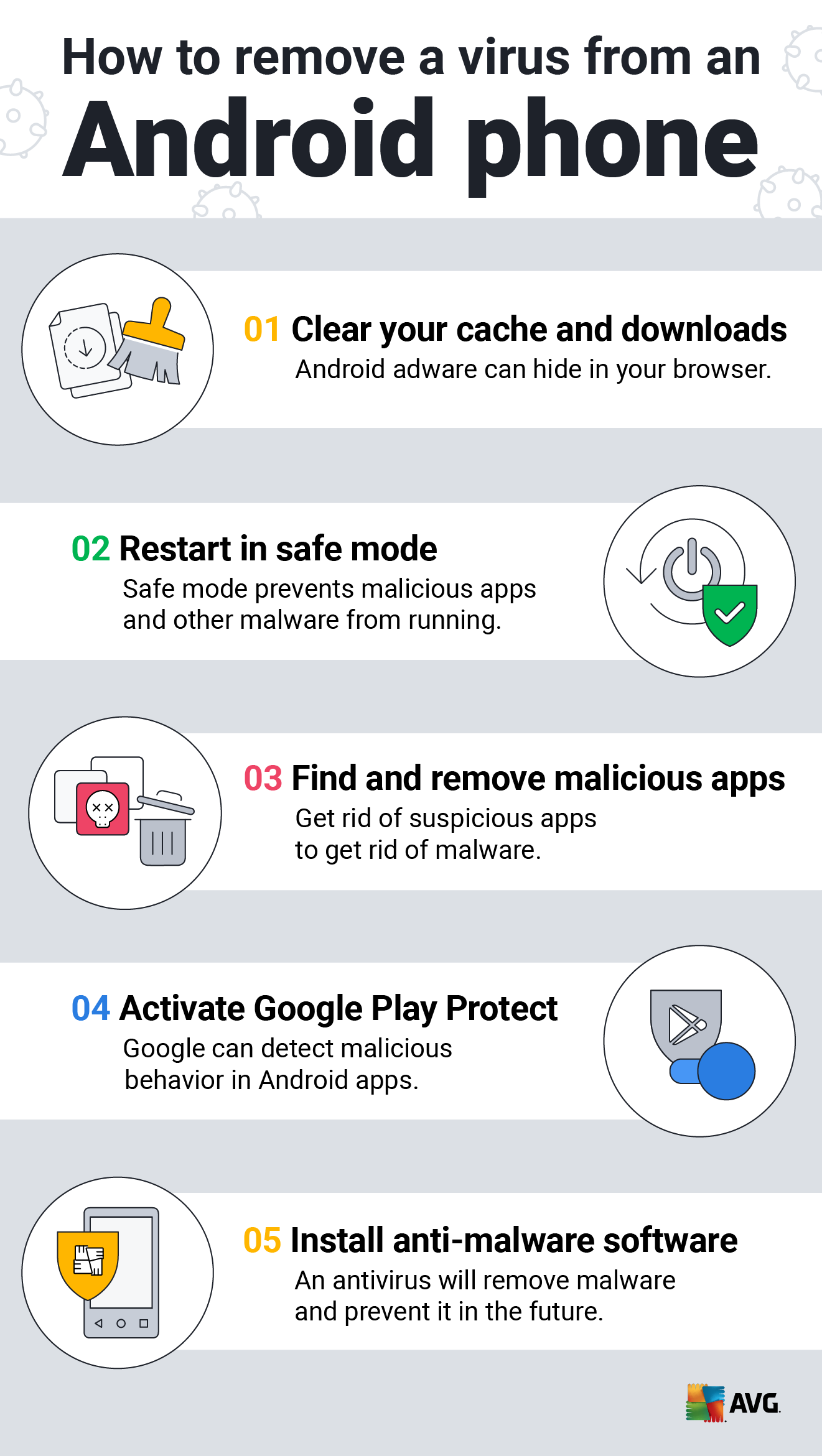
How to Clean an Android or iPhone from Viruses for Free

Free Cybersecurity Training and Career Development
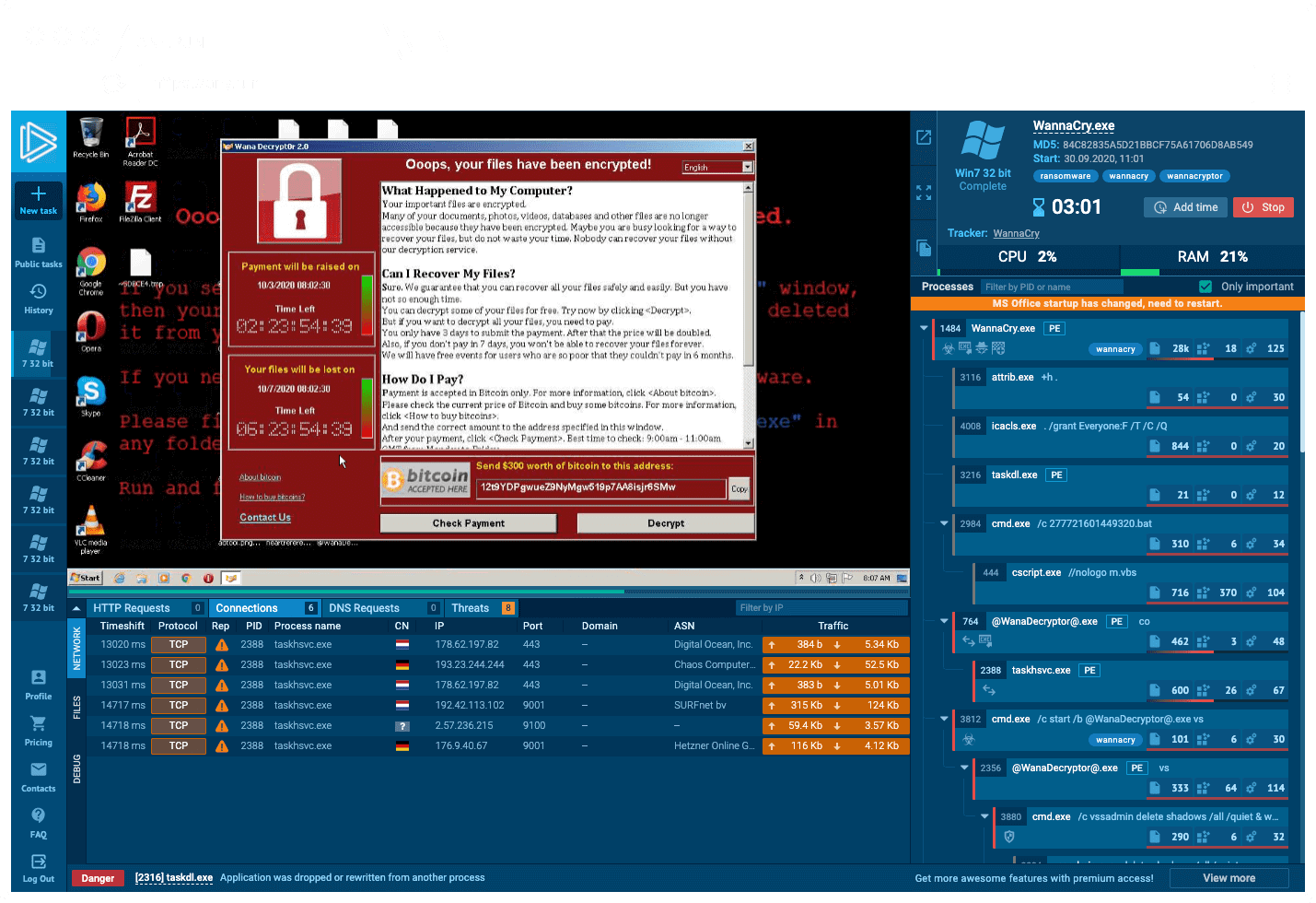
Interactive Online Malware Sandbox
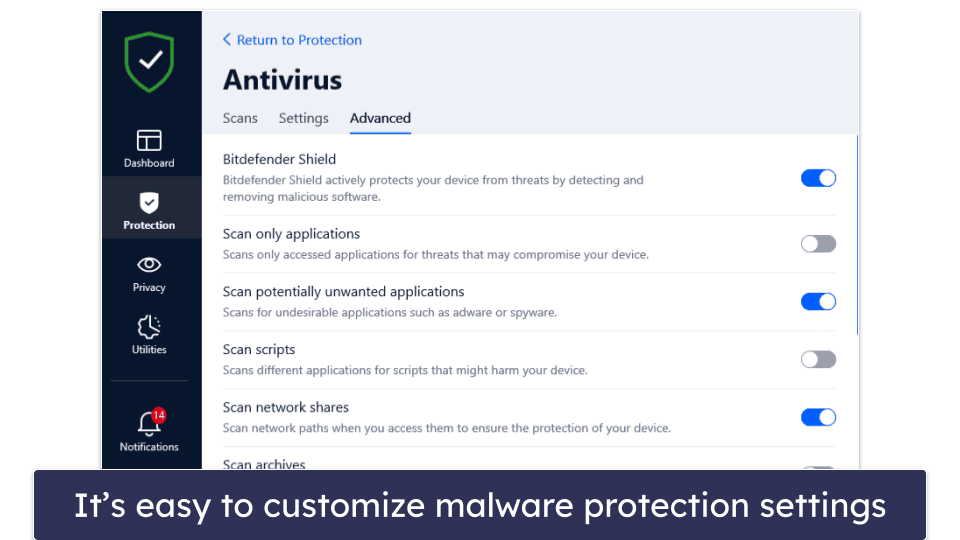
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Feature Extraction and Detection of Malwares Using Machine Learning

MetaDefender Cloud Advanced threat prevention and detection

Malware Analysis: Protecting Your Network from Cyber Attacks

Malware analysis index.html Malicious activity

Cybersecurity Search Engine

Cybersecurity Search Engine

Malware analysis lockysample.bin.zip Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
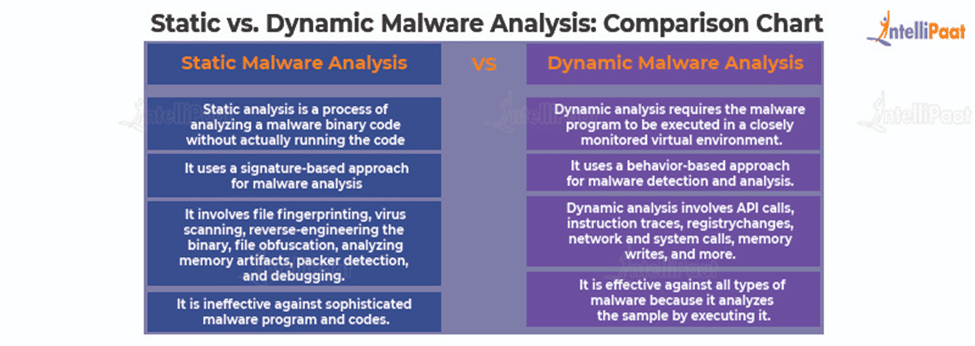
Malware Analysis - What is, Benefits & Types (Easily Explained)

Detail procedure of malware analysis
de
por adulto (o preço varia de acordo com o tamanho do grupo)







