Malware analysis Malicious activity
Por um escritor misterioso
Descrição

A detailed analysis of the Menorah malware used by APT34
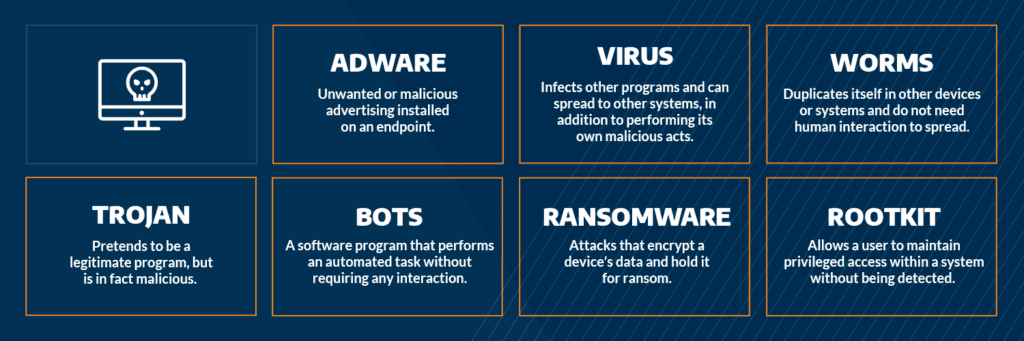
Most Common Malware Attacks
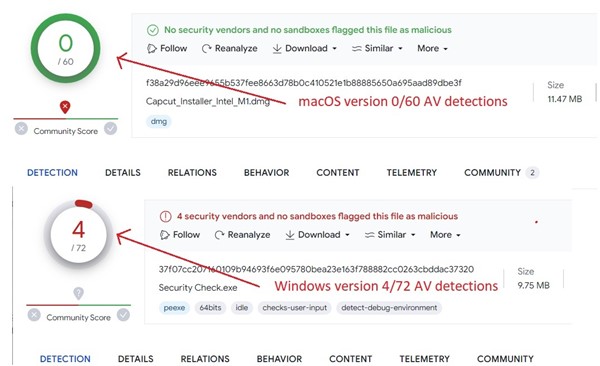
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

Cybersecurity Search Engine

PROUD-MAL: static analysis-based progressive framework for deep

MetaDefender Cloud Advanced threat prevention and detection

MetaDefender Cloud Advanced threat prevention and detection

Routers Roasting on an Open Firewall: the KV-botnet Investigation
Download Free Antivirus Software

StopRansomware: Rhysida Ransomware

Detail procedure of malware analysis

What to Include in a Malware Analysis Report

What is Malware? Definition, Types, Prevention - TechTarget

Malware Analysis: Steps & Examples - CrowdStrike
de
por adulto (o preço varia de acordo com o tamanho do grupo)