How to enforce consistent code scanning rules across Checkov and
Por um escritor misterioso
Descrição
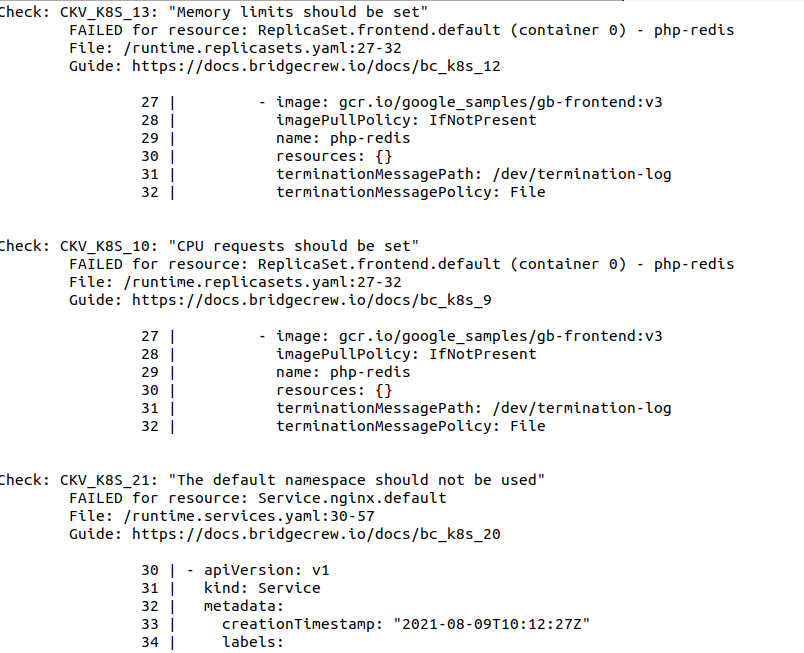
Learn how to create customized and consistent code security scanning rules across the Bridgecrew platform and Checkov.
A Lap around Kubernetes Security & Vulnerability scanning Tools — checkov, kube-hunter, kube-bench & Starboard, by Cloud Journeys with Anindita

Checkov Secrets Scanning: Find exposed credentials in IaC - Bridgecrew Blog
DevSecOps with AWS - Multi Environment deployments- Part 3 - DEV Community

On EKS and Delivery Pipelines, by Dirk Michel

Infrastructure as Code (IaC) Scanning for Vulnerabilities

Best Practices for Scanning and Securing Infrastructure as Code (IaC)[cheat sheet included]
DZone: Programming & DevOps news, tutorials & tools
Top 11 Open-Source Kubernetes Security Tools

Create a Custom policy of Checkov for Kubernetes and Helm, by Rushabh Mahale
20 Essential DevOps Security Best Practices
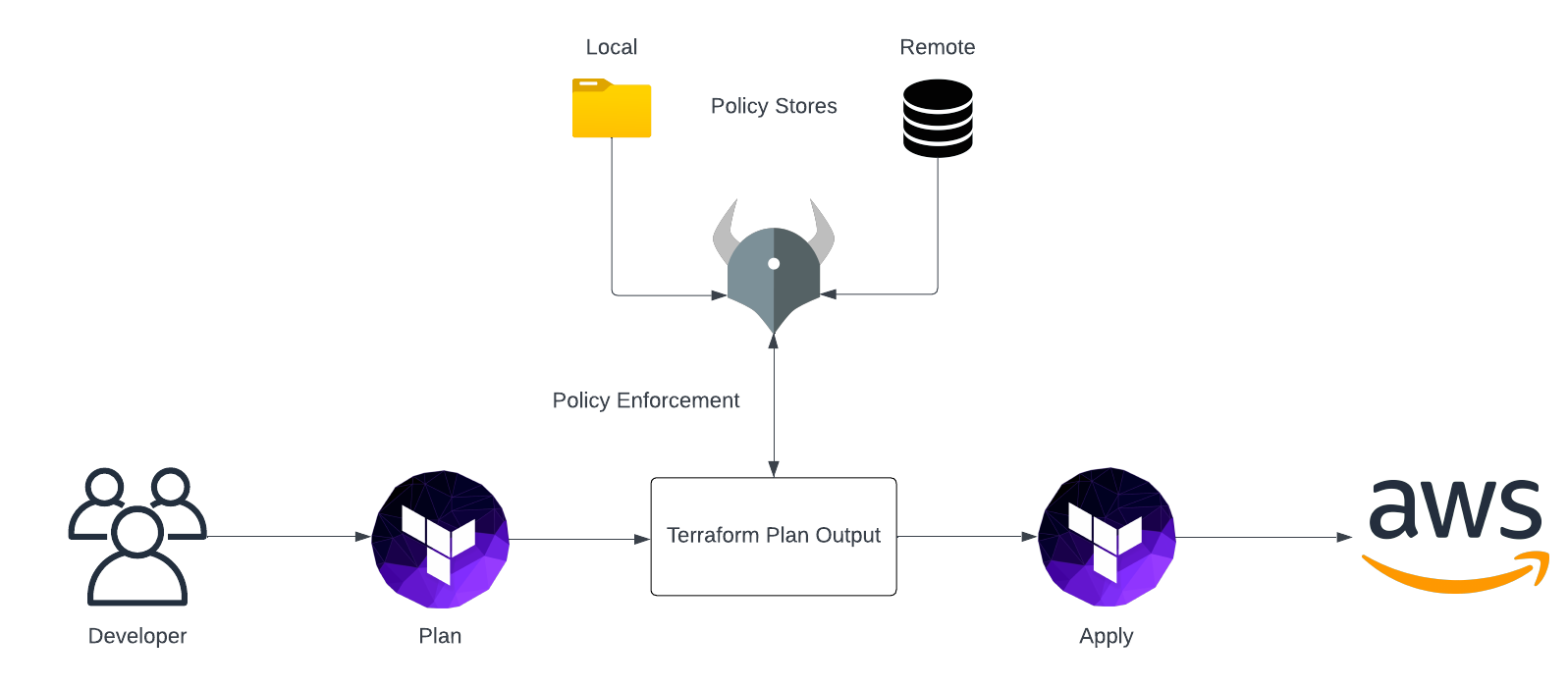
Open Policy Agent for AWS and Terraform
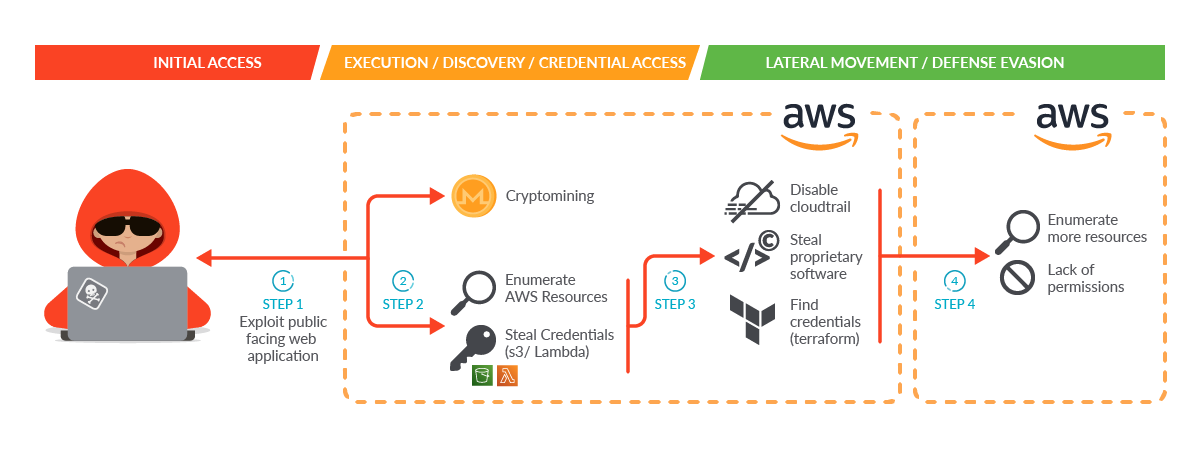
Terraform Security Best Practices – Sysdig

Best Practices for Scanning and Securing Infrastructure as Code (IaC)[cheat sheet included]
de
por adulto (o preço varia de acordo com o tamanho do grupo)