Delay-CJ: A novel cryptojacking covert attack method based on
Por um escritor misterioso
Descrição
Cryptojacking is a type of resource embezzlement attack, wherein an attacker secretly executes the cryptocurrency mining program in the target host to…

PSAK: A provably secure authenticated key agreement scheme based on extended Chebyshev chaotic maps for smart grid environments - Wang - 2023 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
Variants of Crypto-Jacking Attacks and Their Detection Techniques

SHAOYING LIU (Graduate School of Advanced Science and Engineering)

Comparison of CPU usage of browser without and with browser mining
Applied Sciences, Free Full-Text

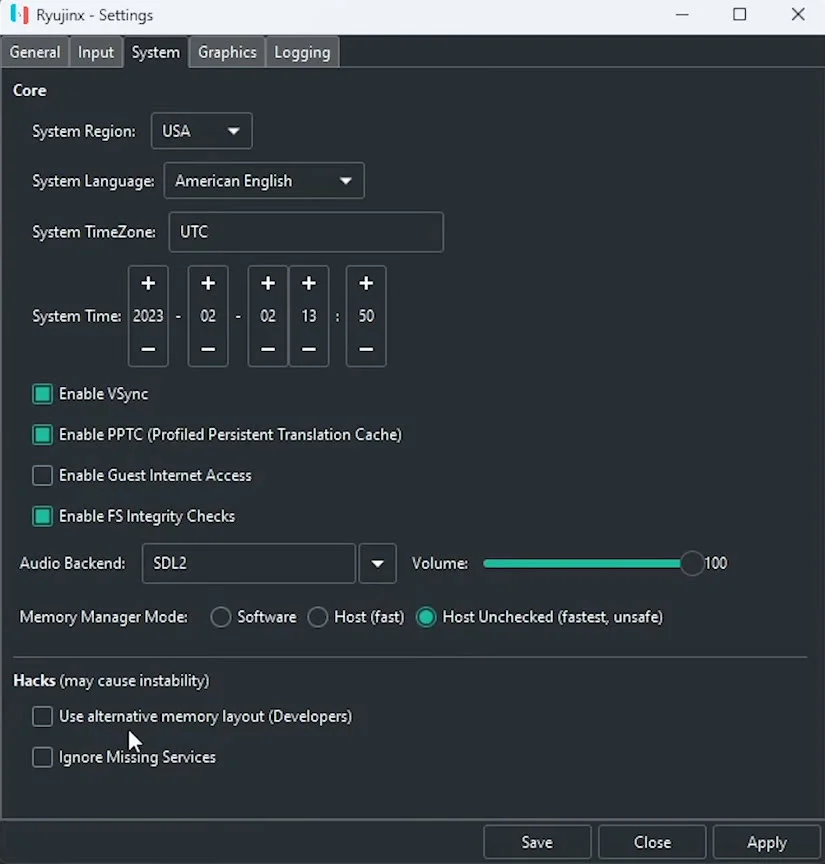
SVM stratified 10-fold cross validation
RAID 2022 – The 25th International Symposium on Research in Attacks, Intrusions and Defenses

PDF) A deep learning approach for host-based cryptojacking malware detection

PDF) A deep learning approach for host-based cryptojacking malware detection

PDF] CoinPolice: Detecting Hidden Cryptojacking Attacks with Neural Networks

PDF] CoinPolice: Detecting Hidden Cryptojacking Attacks with Neural Networks
de
por adulto (o preço varia de acordo com o tamanho do grupo)